Strong Passwords Keep Your Business Safe
We have all had the same frustration. You are busy working on a project at your computer, you open an app or navigate somewhere online to a tool you need to use and you are prompted to update or change your password. But you can’t remember your old password so you can’t change the old password.
Now the task you were trying to perform will take longer because you can’t remember your password!
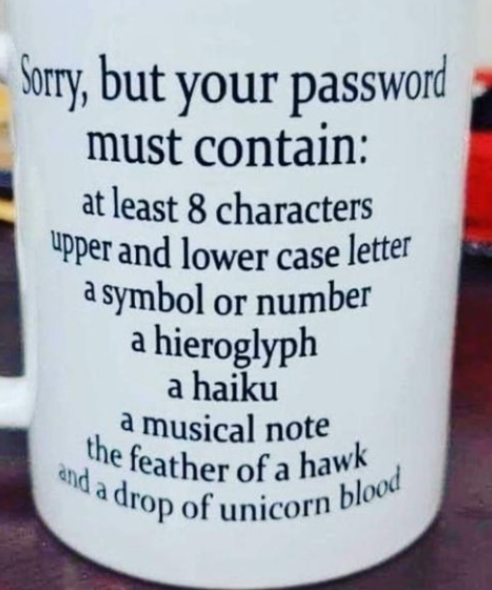
Then when you finally find your old password, you are given a list of instructions on what your new password must contain:
- a minimum of 1 lower case letter [a-z]
- a minimum of 1 upper case letter [A-Z]
- a minimum of 1 numeric character [0-9]
- a minimum of 1 special character: ~`!
Once you manage to meet the password criteria, you then must figure out where you will store the new password. It seems daunting when all you were trying to do was get some work done.
But the truth is, cybercrime incidents are at an all time high, changing your password often and using a strong password is a must in keeping your business safe nowadays.
Do I Really Have To Have Strong Passwords?
One of the main commonalities in ransomware attacks, data breaches and compromised devices is weak passwords.
Recent polls from Google and Verizon show how big the problem really is with weak and unchanged passwords.
81% of cybercrime involved compromised passwords
75% of users are annoyed with trying to keep track of their passwords
25% still use “abc123” or “password123” for their login credentials
66% use their child, pet or spouses name
>40% of compromised passwords still haven’t been changed – (are you kidding me?)
>45% have shared their passwords with a co-worker

In general, users don’t realize how big of a problem weak or unchanged passwords really are and the security risks it poses.
They see changing their passwords as a time-consuming hassle and so they continue to use the same easily hackable password over and over again. I understand why this happens, it’s just that a business and its data need to be secured. Unfortunately, it is hard to change these bad behaviors in users.
To help solve “bad user behavior” and reduce your risk of ransomware attacks, data breaches and compromised devices, implementing multi-factor authentication (MFA) and a password lockout policy reduces your risk of an attack.
What is Multi-Factor Authentication (MFA) and How Does It Work?
MFA is a method to electronically authenticate a user. The user is granted access to an application or website after they have successfully presented two or more items of proof that only the user knows.
The user can provide this proof by using one of several methods:
- Text
- Phone
- Two-factor Authentication App
Once the user is verified, they are given access to the website or app.
So, if a hacker is attempting to break into a website or app of one of your employees, the employee would get a notification asking them to provide their credentials to log into the website or app that the hacker is trying to breach.
Your employee would deny the request and the hacker would be denied access. Stopping a hacker dead in their tracks.
You can see how powerful MFA is in combating cybercriminals from gaining access to your companies’ vital data. It must be a part of your overall cybersecurity plan to help you stay protected.
Password Lockout Policy – What Is It?
The purpose of a password lockout policy is to disrupt the bots that are attempting to guess your password.
This is accomplished by locking an account for fifteen minutes when a wrong password is entered 3 – 5 times. When the account is locked the bot is blocked from entering any more passwords for fifteen minutes. Otherwise, the bots can hack away until they guess your password.
During the fifteen minutes, the user of the account receives a notification that their account has been locked alerting them of a potential problem.
As you can see, by using these two simple security measures (MFA and Password Lockout) you can add layers of protection to your business that keep it and your data safe. It’s all part of a solid cybersecurity plan.
How Can I Ensure I Can Keep My Business Protected?
You must have a cybersecurity plan in place to keep your business safe and protected. A good cybersecurity plan includes ongoing employee cybersecurity training and an experienced IT partner to help you assess your companies’ vulnerabilities and implement them for you.
Cybersecurity Training
Hackers are good at what they do and are constantly inventing new ways to gain access to your valuable data. The first line of attack is through your employees. Cybercriminals are relentless in their attempts and will try anything to get usernames and passwords from your employees.
Ongoing cybersecurity training helps your employees spot these attempts and gives them a process to follow when something looks wrong or out of place.
For more information on Cybersecurity training also see:
The Five Ways to Hack Your Business Email
The Cost of Downtime and the Effects of Ransomware on Small Business
Your Best Odds of Stopping Phishing Attacks Cold
An Experienced IT Partner
Let’s face it, it takes a lot to run a business and there is not enough time to learn how to do everything yourself – and your business’s cybersecurity is not an easy task. Plus, it’s a real pain having to keep up with various passwords for your employees (current, new and old) and all the different applications, networks, vpns, and other technology you need to use every day. But it’s critical to protecting your business.
It takes a lot to secure what’s in your office, but when you factor in your remote workers, vendors, sub-contractors and partners you suddenly realize the job of securing your business is gigantic.
That’s why you need an experienced IT partner like Attain Technology to keep you safe and protected.
If you are ready to protect your employees and your business or need help assessing your company’s vulnerabilities and weaknesses, you can schedule a free Technology Audit with me here: https://attaintechnology.com/construction-technology-audit/


